
Benefits
Specifications
How-to
Contact Us
Learn More
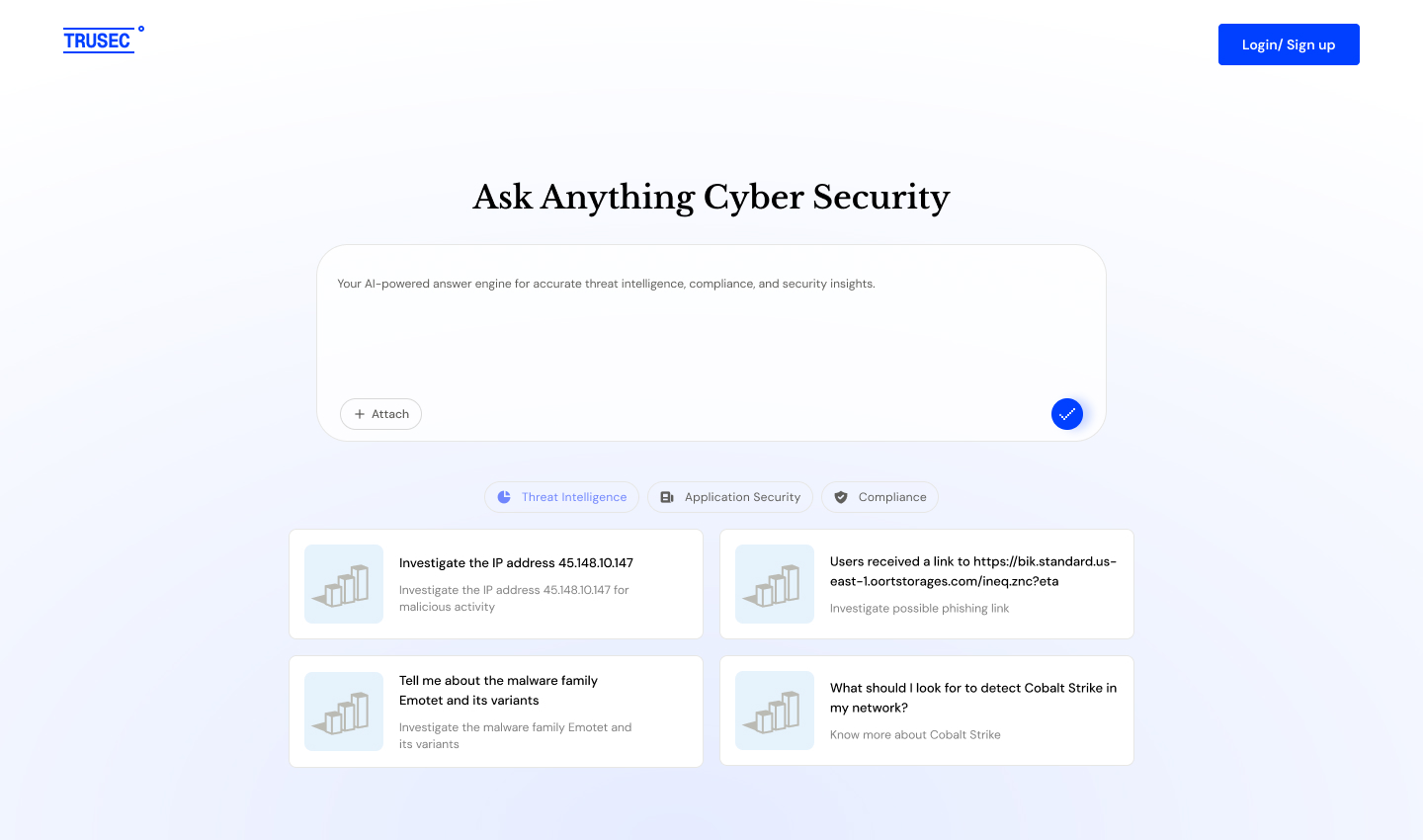
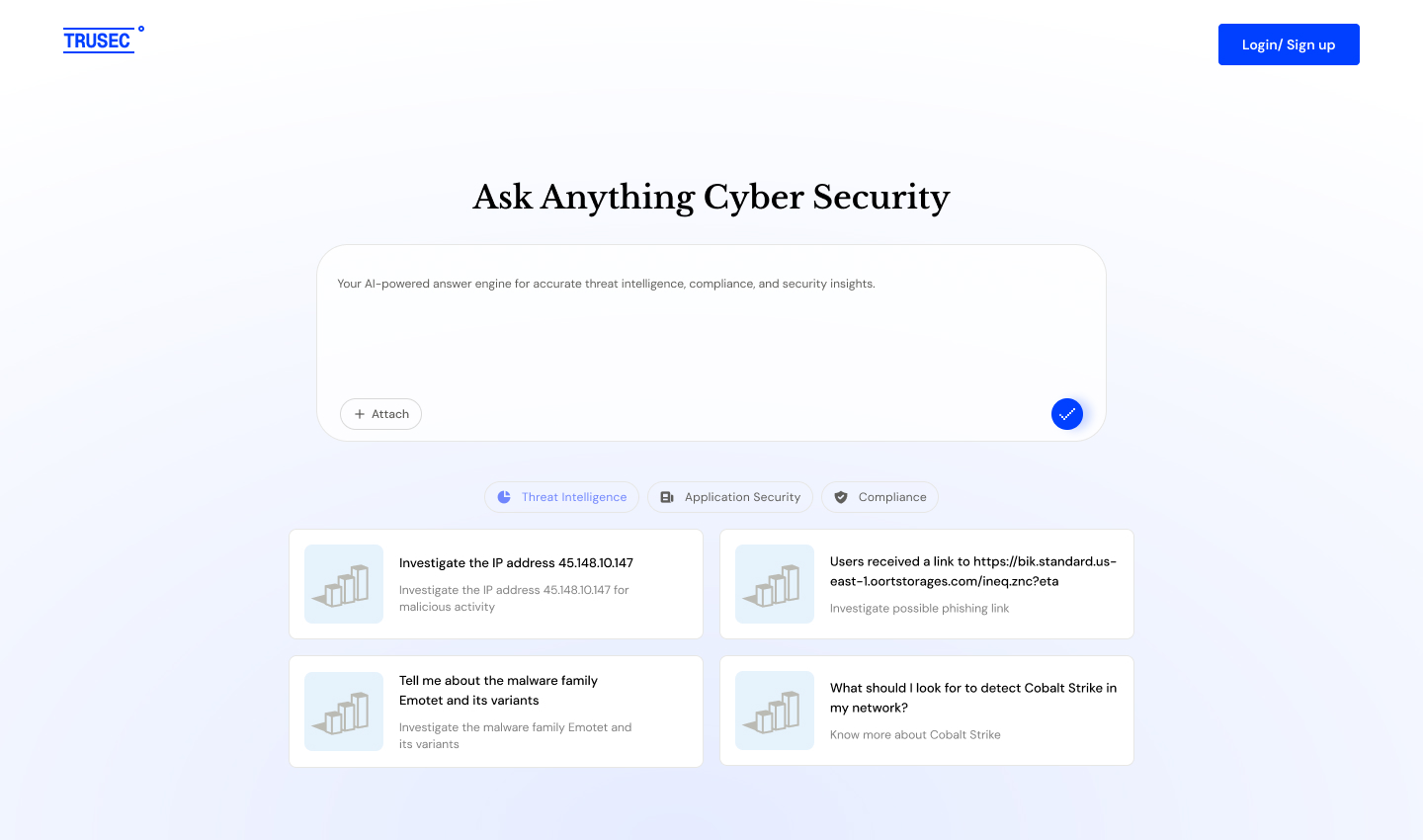
Ask Anything
Cyber Security
Your AI-powered answer engine for accurate threat intelligence, compliance, and security insights.
Contact Us
Ask your Questions
“A specialized security research engine that delivers evidence-cited, up-to-date, expert-level answers across vulnerabilities, threats, techniques, and defenses.”
10x
Faster triage
30-50%
Time saved on research
Ask a question
What You Can Ask TruSec?
From secure coding to threat analysis, TruSec provides expert answers across three key security domains.

Threat Intelligence
"Is this IP address malicious: 192.0.2.1?"
Check against 50+ threat intelligence feeds with reputation scores, associated malware, and historical data.
"Tell me about the Emotet malware family"
Get comprehensive analysis including TTPs, IOCs, distribution methods, and defensive measures.
“What is ransomware and how does it work?"
Understand attack chains, common families, prevention strategies, and incident response procedures.

Compliance & Regulations
What encryption standards does PCI-DSS 4.0 require?
Get specific cryptographic requirements, key lengths, algorithm deprecations, and implementation guidance for payment data protection.
Do we need DPO for GDPR if we process 10K EU records?
Understand GDPR Article 37 applicability thresholds, processing volume considerations, systematic monitoring criteria, and DPO appointment requirements.
What are SOC 2 logging requirements for audit trails?
Learn about CC7.2 control criteria, log retention periods, integrity monitoring, and what events must be captured for compliance.

Application Security
Is CVE-2024-1234 exploited in the wild?
Get real-world exploitability assessment with KEV status, active campaigns, PoC availability, and affected version details with mitigation controls.
What OWASP controls mitigate SQL injection in Node.js?
Receive specific code examples, prepared statements for popular ORMs, input validation patterns, and secure coding best practices with OWASP A03 mapping.
Explain SSRF attacks and prevention in cloud environments
Learn attack vectors specific to AWS/Azure metadata services, IMDSv2 requirements, network policies, and cloud-specific defense strategies.
Specs
Why Choose Trusec?
TruSec reasons like a security analyst. TruSec is trained and optimized exclusively for security workflows.
Feature
Security Expertise
Data & Training
Freshness
Speed
Context Awareness
Usability
Purpose-built for cybersecurity with deep domain context
Trained on security-specific data
Real-time threat intelligence from 50+ sources
Instant, comprehensive answers
Conversational, remembers context and follow-ups
Ask, refine, and explore naturally
Generic AI Search
Generic web sources
No domain structure
Outdated blogs and SEO-ranked content
Manual scanning across multiple links
No exploitation context
Repeated keyword searches
Knowledge Source
Security-Specific Reasoning Engine
Access real-time threat data from over 50 trusted sources. TruSec aggregates and correlates intelligence to provide actionable insights for your security operations.
01
Real-time Updates: Continuous synchronization with threat intelligence feeds
02
Contextual Analysis: AI-powered correlation across multiple threat sources
03
Custom Integration: Add your organization-specific threat intelligence feeds
Features
Powerful Features for Modern Security Teams
From threat intelligence to automated response, TruSec provides everything you need to stay ahead of cyber threats.
Intelligent Chat Interface
Chat UI with conversation history, suggested follow-ups, and natural language queries for threat investigation.
Actionable Guidance
Deliver accurate security insights, step-by-step implementation guidance, risk mitigation strategies, and up-to-date threat intelligence.
Deep Threat Investigation
Analyze IOCs, investigate threats and malware, perform forensic analysis, and correlate security events to uncover attack patterns.
Security Knowledge & Best Practices
SOAR Capabilities
Execute automated response actions with human-in-the-loop approval mechanisms and status updates back to your SIEM/JIRA tickets.

Coming Soon
Seamlessly Integrate





Get professional-grade, security researched answers!
Join SOC analysts, AppSec engineers, and security teams who trust TruSec for fast, accurate, evidence-cited security intelligence.
support@trusec.io
Ask Anything
Cyber Security
Your AI-powered answer engine for accurate threat intelligence, compliance, and security insights.
Contact Us
Ask your Questions
“A specialized security research engine that delivers evidence-cited, up-to-date, expert-level answers across vulnerabilities, threats, techniques, and defenses.”
10x
Faster triage
30-50%
Time saved on research
Ask a question
What You Can Ask TruSec?
From secure coding to threat analysis, TruSec provides expert answers across three key security domains.

Threat Intelligence
"Is this IP address malicious: 192.0.2.1?"
Check against 50+ threat intelligence feeds with reputation scores, associated malware, and historical data.
"Tell me about the Emotet malware family"
Get comprehensive analysis including TTPs, IOCs, distribution methods, and defensive measures.
“What is ransomware and how does it work?"
Understand attack chains, common families, prevention strategies, and incident response procedures.

Compliance & Regulations
What encryption standards does PCI-DSS 4.0 require?
Get specific cryptographic requirements, key lengths, algorithm deprecations, and implementation guidance for payment data protection.
Do we need DPO for GDPR if we process 10K EU records?
Understand GDPR Article 37 applicability thresholds, processing volume considerations, systematic monitoring criteria, and DPO appointment requirements.
What are SOC 2 logging requirements for audit trails?
Learn about CC7.2 control criteria, log retention periods, integrity monitoring, and what events must be captured for compliance.

Application Security
Is CVE-2024-1234 exploited in the wild?
Get real-world exploitability assessment with KEV status, active campaigns, PoC availability, and affected version details with mitigation controls.
What OWASP controls mitigate SQL injection in Node.js?
Receive specific code examples, prepared statements for popular ORMs, input validation patterns, and secure coding best practices with OWASP A03 mapping.
Explain SSRF attacks and prevention in cloud environments
Learn attack vectors specific to AWS/Azure metadata services, IMDSv2 requirements, network policies, and cloud-specific defense strategies.
Specs
Why Choose Trusec?
TruSec reasons like a security analyst. TruSec is trained and optimized exclusively for security workflows.
Feature
Security Expertise
Data & Training
Freshness
Speed
Context Awareness
Usability
Purpose-built for cybersecurity with deep domain context
Trained on security-specific data
Real-time threat intelligence from 50+ sources
Instant, comprehensive answers
Conversational, remembers context and follow-ups
Ask, refine, and explore naturally
Generic AI Search
Generic web sources
No domain structure
Outdated blogs and SEO-ranked content
Manual scanning across multiple links
No exploitation context
Repeated keyword searches
Knowledge Source
Security-Specific Reasoning Engine
Access real-time threat data from over 50 trusted sources. TruSec aggregates and correlates intelligence to provide actionable insights for your security operations.
01
Real-time Updates: Continuous synchronization with threat intelligence feeds
02
Contextual Analysis: AI-powered correlation across multiple threat sources
03
Custom Integration: Add your organization-specific threat intelligence feeds
Features
Powerful Features for Modern Security Teams
From threat intelligence to automated response, TruSec provides everything you need to stay ahead of cyber threats.
Intelligent Chat Interface
Chat UI with conversation history, suggested follow-ups, and natural language queries for threat investigation.
Security Knowledge & Best Practices
SOAR Capabilities
Execute automated response actions with human-in-the-loop approval mechanisms and status updates back to your SIEM/JIRA tickets.
Actionable Guidance
Deliver accurate security insights, step-by-step implementation guidance, risk mitigation strategies, and up-to-date threat intelligence.
Deep Threat Investigation
Analyze IOCs, investigate threats and malware, perform forensic analysis, and correlate security events to uncover attack patterns.

Coming Soon
Seamlessly Integrate





Get professional-grade, security researched answers!
Join SOC analysts, AppSec engineers, and security teams who trust TruSec for fast, accurate, evidence-cited security intelligence.
support@trusec.io
Ask Anything
Cyber Security
Your AI-powered answer engine for accurate threat intelligence, compliance, and security insights.
Contact Us
Ask your Questions
“A specialized security research engine that delivers evidence-cited, up-to-date, expert-level answers across vulnerabilities, threats, techniques, and defenses.”
10x
Faster triage
30-50%
Time saved on research
Ask a question
What You Can Ask TruSec?
From secure coding to threat analysis, TruSec provides expert answers across three key security domains.

Threat Intelligence
"Is this IP address malicious: 192.0.2.1?"
Check against 50+ threat intelligence feeds with reputation scores, associated malware, and historical data.
"Tell me about the Emotet malware family"
Get comprehensive analysis including TTPs, IOCs, distribution methods, and defensive measures.
“What is ransomware and how does it work?"
Understand attack chains, common families, prevention strategies, and incident response procedures.

Compliance & Regulations
What encryption standards does PCI-DSS 4.0 require?
Get specific cryptographic requirements, key lengths, algorithm deprecations, and implementation guidance for payment data protection.
Do we need DPO for GDPR if we process 10K EU records?
Understand GDPR Article 37 applicability thresholds, processing volume considerations, systematic monitoring criteria, and DPO appointment requirements.
What are SOC 2 logging requirements for audit trails?
Learn about CC7.2 control criteria, log retention periods, integrity monitoring, and what events must be captured for compliance.

Application Security
Is CVE-2024-1234 exploited in the wild?
Get real-world exploitability assessment with KEV status, active campaigns, PoC availability, and affected version details with mitigation controls.
What OWASP controls mitigate SQL injection in Node.js?
Receive specific code examples, prepared statements for popular ORMs, input validation patterns, and secure coding best practices with OWASP A03 mapping.
Explain SSRF attacks and prevention in cloud environments
Learn attack vectors specific to AWS/Azure metadata services, IMDSv2 requirements, network policies, and cloud-specific defense strategies.
Specs
Why Choose Trusec?
TruSec reasons like a security analyst. TruSec is trained and optimized exclusively for security workflows.
Feature
Security Expertise
Data & Training
Freshness
Speed
Context Awareness
Usability
Purpose-built for cybersecurity with deep domain context
Trained on security-specific data
Real-time threat intelligence from 50+ sources
Instant, comprehensive answers
Conversational, remembers context and follow-ups
Ask, refine, and explore naturally
Generic AI Search
Generic web sources
No domain structure
Outdated blogs and SEO-ranked content
Manual scanning across multiple links
No exploitation context
Each search starts from scratch
Knowledge Source
Security-Specific Reasoning Engine
Access real-time threat data from over 50 trusted sources. TruSec aggregates and correlates intelligence to provide actionable insights for your security operations.
01
Real-time Updates: Continuous synchronization with threat intelligence feeds
02
Contextual Analysis: AI-powered correlation across multiple threat sources
03
Custom Integration: Add your organization-specific threat intelligence feeds
Features
Powerful Features for Modern Security Teams
From threat intelligence to automated response, TruSec provides everything you need to stay ahead of cyber threats.
Intelligent Chat Interface
Chat UI with conversation history, suggested follow-ups, and natural language queries for threat investigation.
Security Knowledge & Best Practices
Explain security standards, guide policies and compliance, cover cloud, application, and infrastructure security, and highlight emerging threats.
Actionable Guidance
Deliver accurate security insights, step-by-step implementation guidance, risk mitigation strategies, and up-to-date threat intelligence.
Deep Threat Investigation
Analyze IOCs, investigate threats and malware, perform forensic analysis, and correlate security events to uncover attack patterns.

Coming Soon
Seamlessly Integrate





Get professional-grade, security researched answers!
Join SOC analysts, AppSec engineers, and security teams who trust TruSec for fast, accurate, evidence-cited security intelligence.



